SSO Microsoft 365 su iOS ed iPadOS
Zero-touch Enrollment and Managed Apple Account
Thanks to Apple Business Manager or Apple School Manager, devices can be configured in a blink of an eye. In fact, after connecting Apple portal with %mdmName%, devices must be switched on and it will receive automatically all the configurations over-the-air.
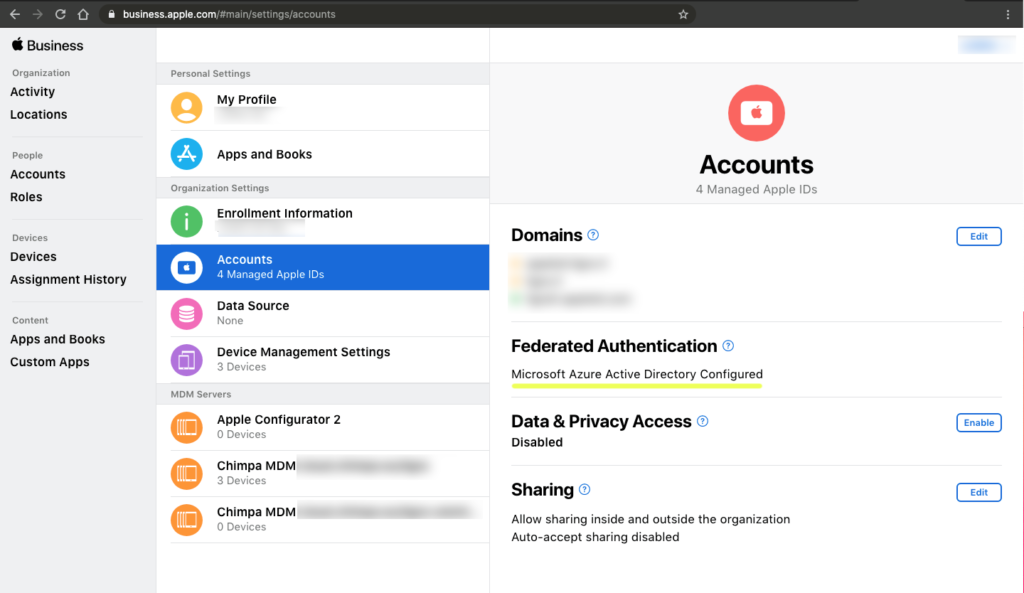
Admin has to enable Azure federation on Apple Business Manager. As a result, users can leverage their Azure AD usernames (User Principal Name) and passwords as Managed Apple Accounts.
MDM Configuration
%mdmName% allows integration with Azure on %whitelabelText2% Admin, so the users can insert their Microsoft account to authorize the Remote Management phase.
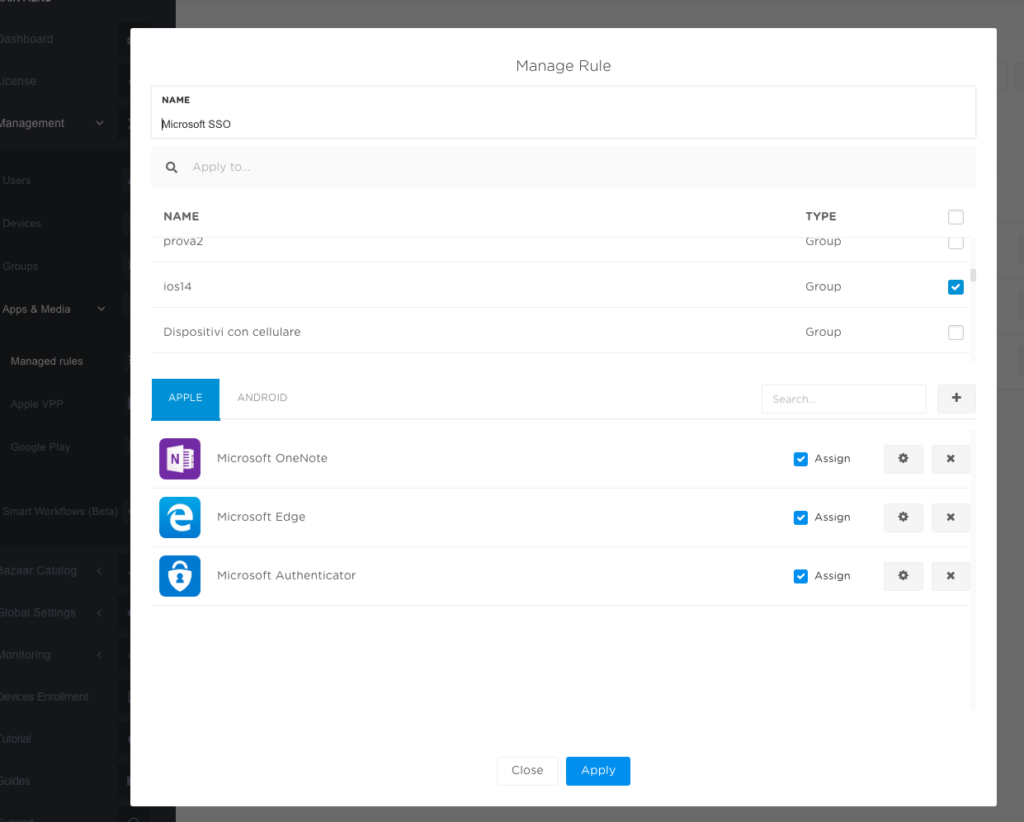
Admin has to create a rule that assigns and auto installs Microsoft Apps from %whitelabelText2% Admin, using VPP licensing.
Note: It is very important that Microsoft Authenticator app is installed because it will manage the SSO procedures.
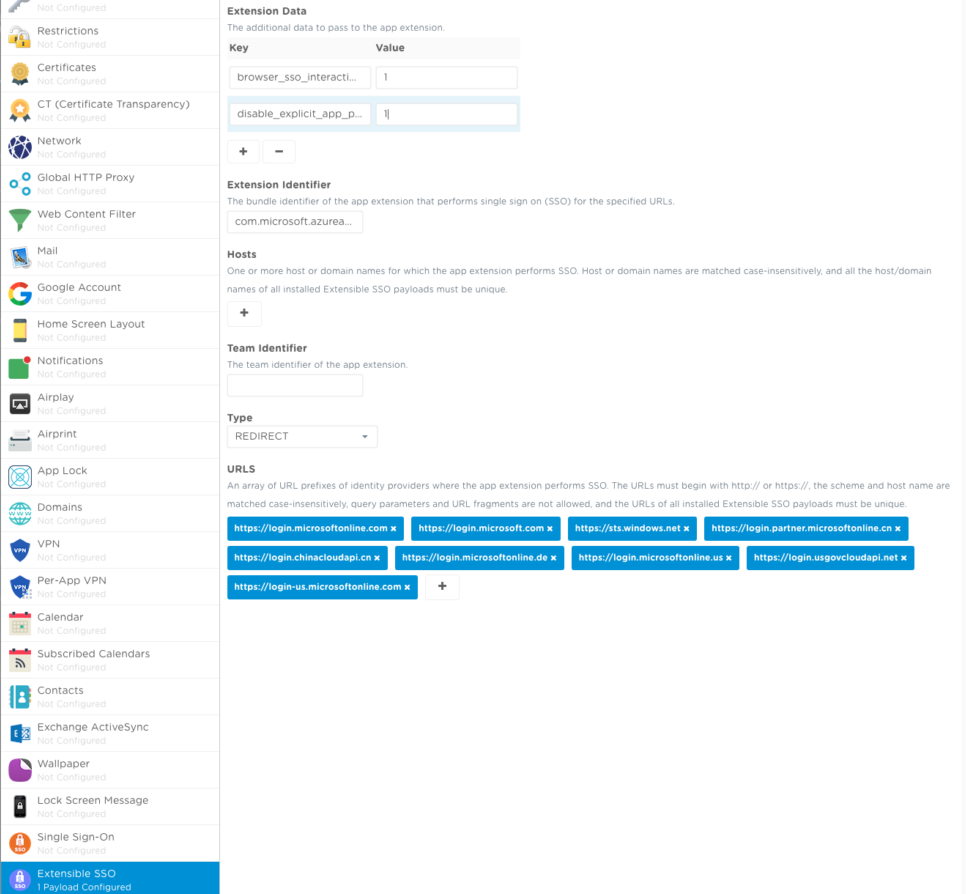
Another thing to do on the %whitelabelText2% Admin is to create a configuration profile containing the Extensible SSO payload, compatible from iOS 13 and iPadOS 13.
Additional info for this configuration are available at this link.
User Experience
At this point, users unbox the new received device that was prepared to follow the zero-touch configuration and the enrollment with %mdmName%.
Follow the Setup Assistant after powering on the device, set country, language, wifi or cellular connection. After some seconds, Remote Management screen will popup. User can easily authenticate via a Microsoft account thanks to the integration between %mdmName% and Azure SSO.
The device has been enrolled on %mdmName% and automatically starts to download work apps, settings and restrictions.
User could add its own Managed Apple Account using Azure federation and, one more time, the Microsoft account in one app.
In fact, after this “last” authentication, Microsoft Authenticator app will assist every access on compatible apps and sites.